Technology
-
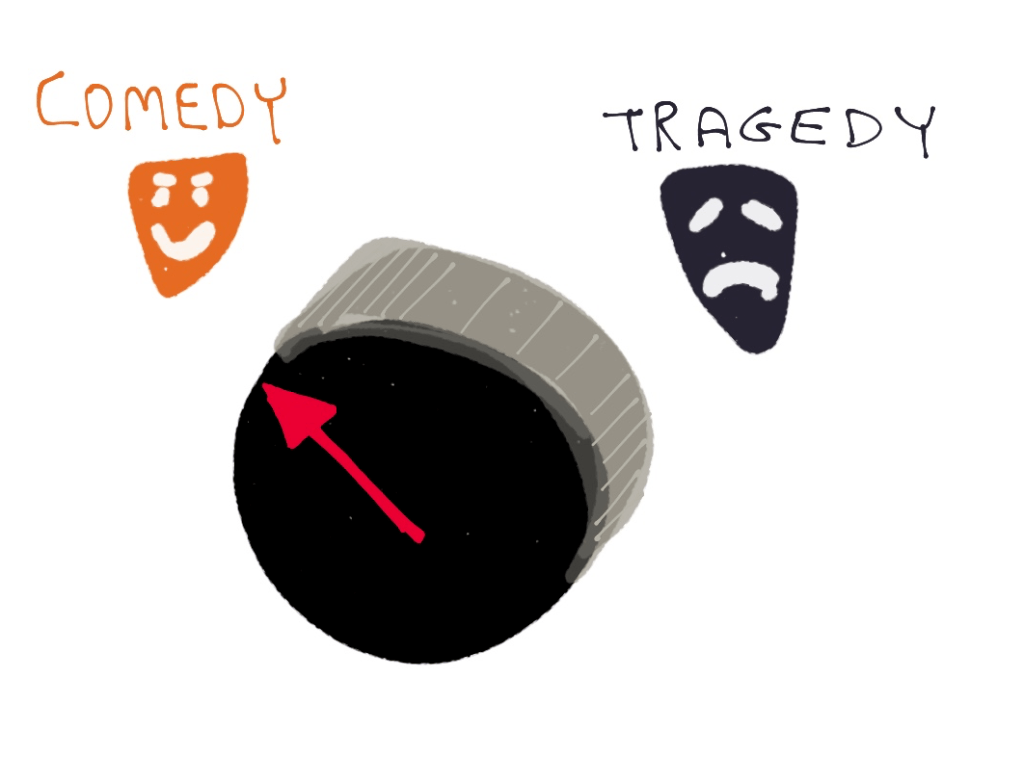
Background: With the introduction of DVDs, it first became possible for a movie to contain user-selectable arrangements of scenes. This was a rarely used feature, but it did have a few interesting applications, such as a feature on the Memento DVD that allowed the movie to be watched in reverse order from normal (i.e., in…
-
One weird application of the “invisible fence” dog collar that’s setting the world of Internet comments on fire! And possibly also setting people on fire, depending on the amperage involved.
dog collar, fix internet comments, hexagon commission, Internet, internet comment shock collar, internet commenting, internet shock collar, invisible fence collar, lizard people, no need for comment moderation with this one weird trick, possible electrocution hazard, quadrilateral commission, shock collar, trilateral commission, usb compatible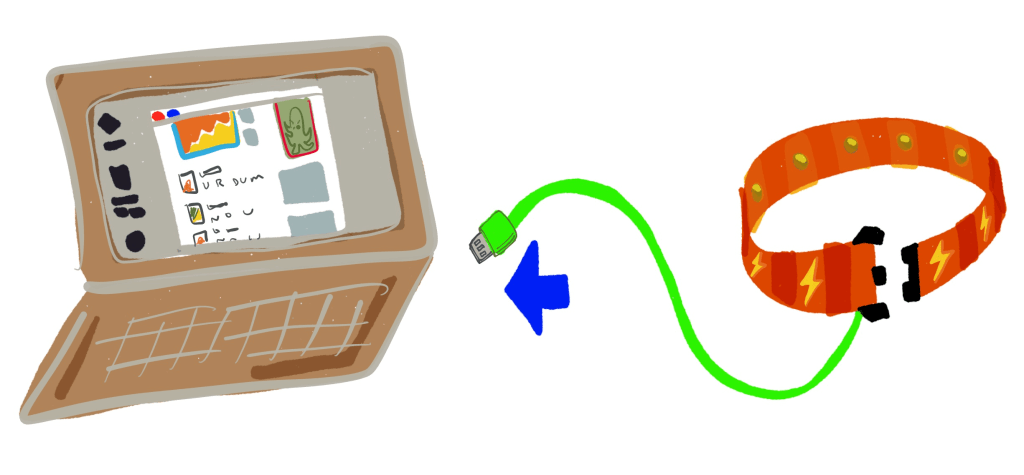
Background: The staggering degree of stupidity and general mean-spiritedness of Internet comments is a well known and undeniable phenomenon. But what can be done to prevent the anonymity of the Internet from causing people to write inhumanly monstrous things in Internet comment sections? Fig 1: Even if your web site is about historical Danish model…
-
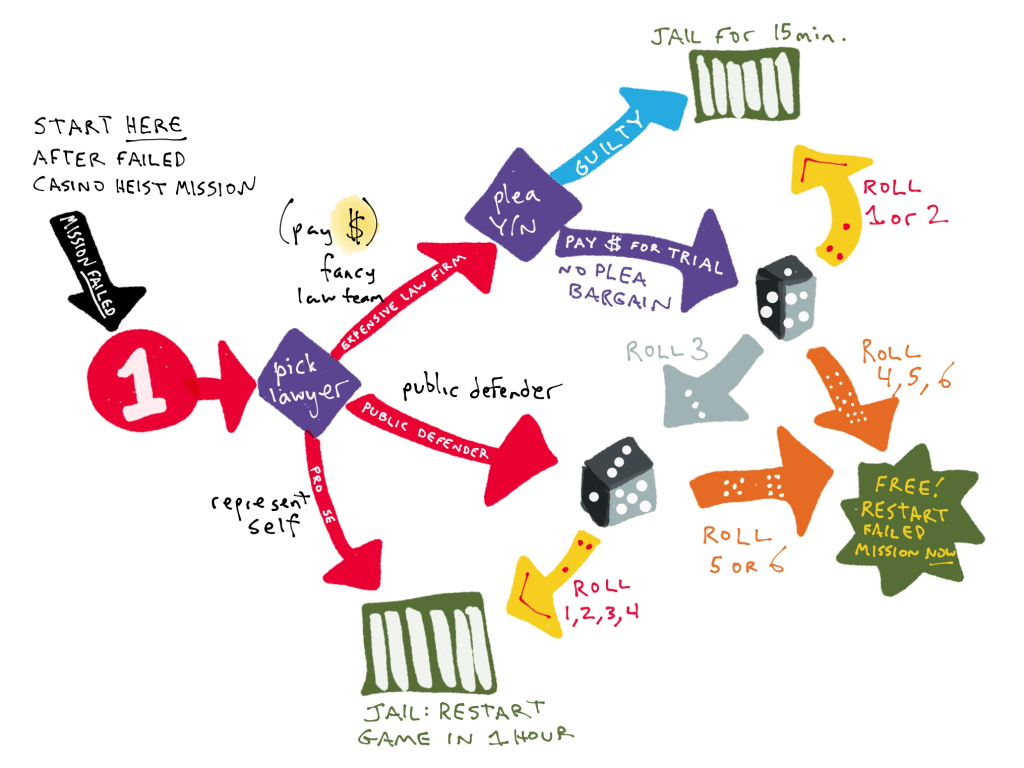
Background: We previously focused on adding a sense of danger to a computer game by adding new consequence for failure. (Specifically, adding an increasingly-onerous delay to the player respawn timer.) In this follow-up idea, we suggest two motivating premises: If a player has no consequences for failure, then they will not as keenly feel…
-

Background: Camouflage is a useful tool for hiding something in a distracting pattern that it blends into. Most frequently, camouflage is used to hide a person (for example, a hunter or soldier) in an environment where they would prefer not to be spotted. Fig 1: Traditional forest camouflage, used to hide from snakes, owls, and…
-
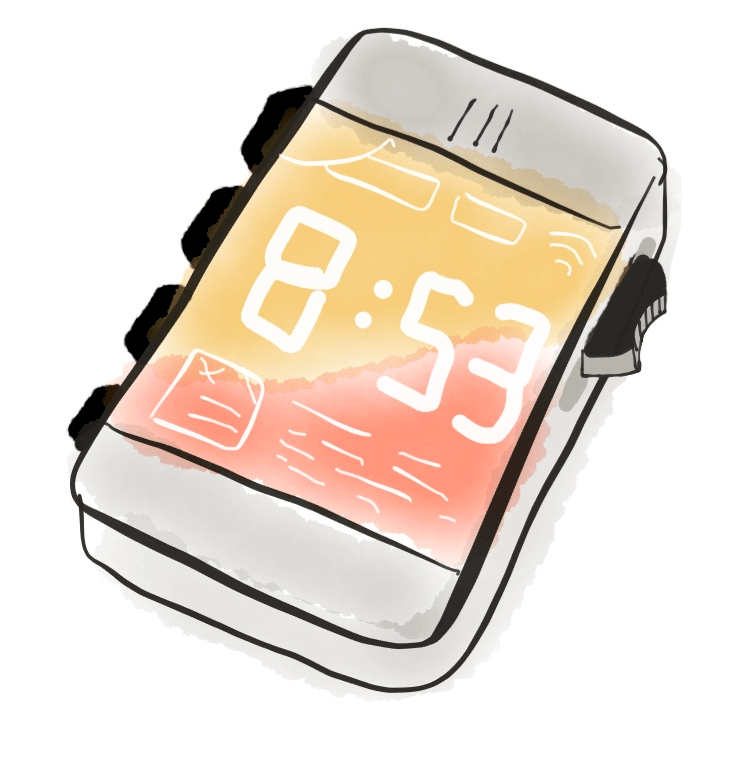
Background: Nearly all modern cell phones have the same touch-screen form factor. Except for a few buttons of low importance (e.g. volume adjustment, power, camera shutter), all interaction is done through the screen itself. The issue: This style of interaction makes use of only one finger, and leaves the remaining four fingers with nothing to…
-

Background: Back in the ancient days before iPhones, people would store files in a hierarchical fashion in “folders” or “directories” on their computers. The issue: Sometimes, despite relatively descriptive folder names, it is not clear what a folder / directory actually is. For example, on Mac OS X, a casual user may be flummoxed by…
-
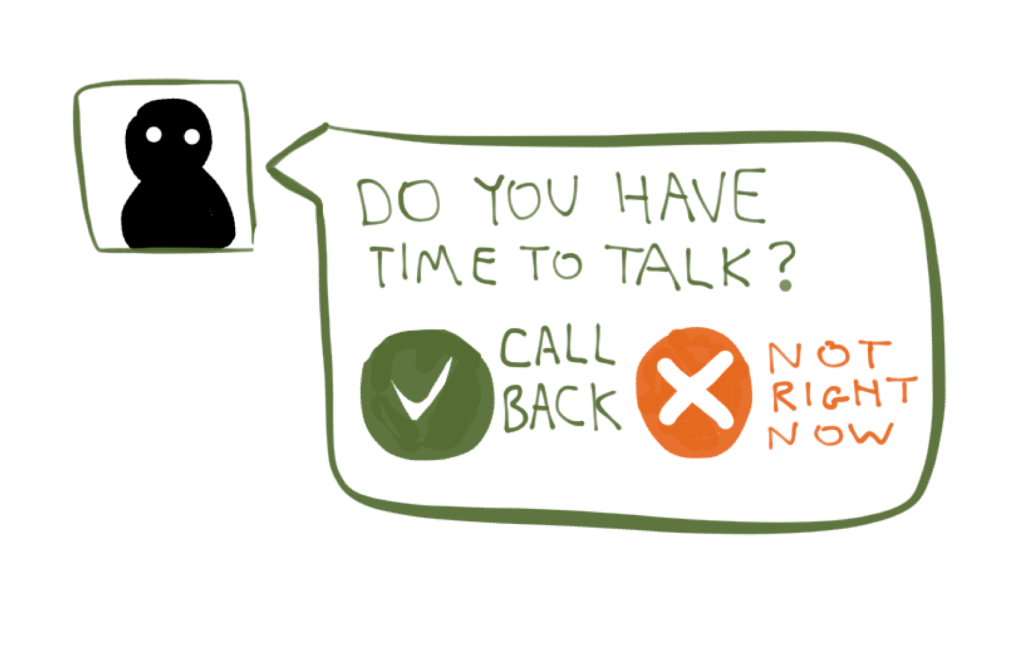
Background: Phone woes: when you use text or call someone, there’s no way to differentiate between the following scenarios: Low priority (not time-sensitive): “Let’s chat, if you have time.” Medium priority (time-sensitive): “I just showed up at the crowded convention center, but I can’t find you.” High priority (important and time-sensitive): “Your car is about to…



You must be logged in to post a comment.