encryption
-
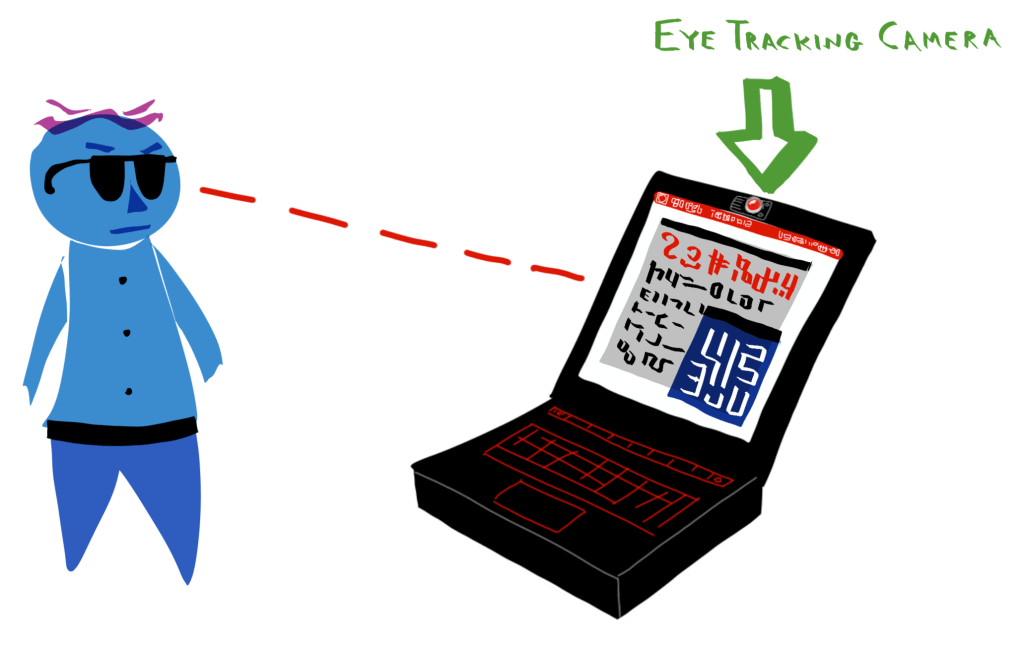
Background: Laptop privacy screens (or “monitor filters”) reduce the viewing angle of a laptop screen in order to prevent evildoers from snooping on sensitive information on your laptop (Figure 1). The issue: Unfortunately, these privacy screens have a few downsides: They are inelegant to attach. Often, the attachment points block a small amount of screen…
-
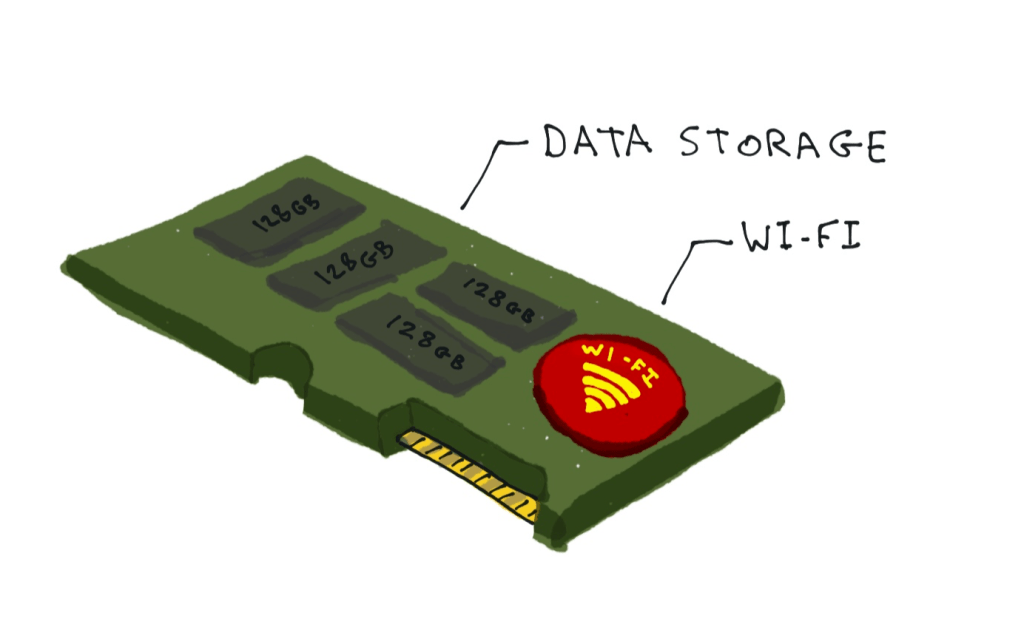
The issue: Currently, the loss or theft of an unencrypted laptop can be a huge pain for an employee and/or their company. If a laptop gets stolen out of a person’s car, or just gets forgotten in a train or cafe, it’s entirely possible that the laptop owner will now have to change all their…

You must be logged in to post a comment.