decryption
-
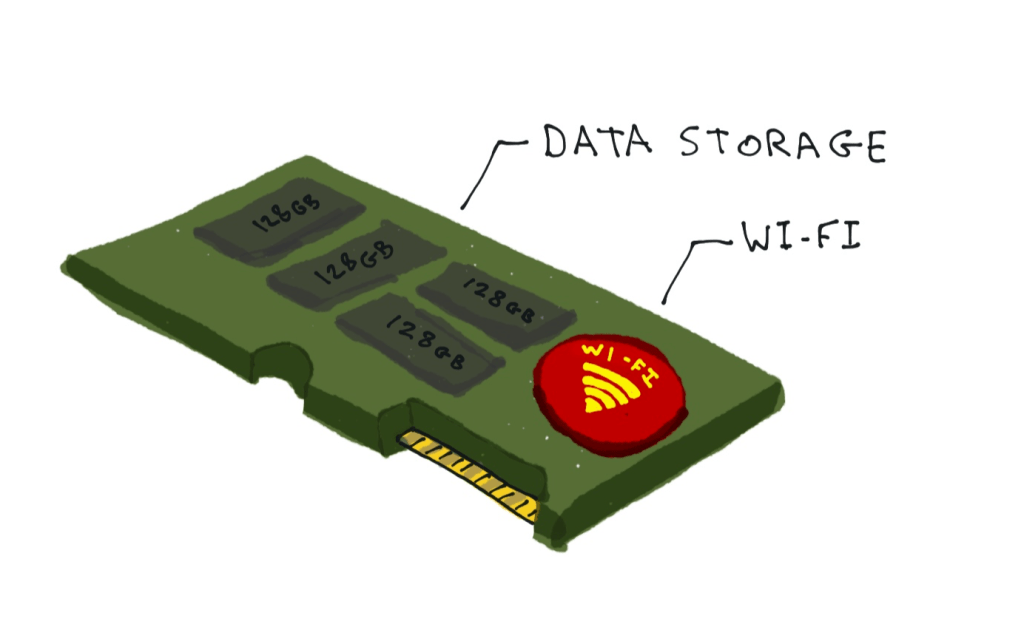
The issue: Currently, the loss or theft of an unencrypted laptop can be a huge pain for an employee and/or their company. If a laptop gets stolen out of a person’s car, or just gets forgotten in a train or cafe, it’s entirely possible that the laptop owner will now have to change all their…

You must be logged in to post a comment.